Get Ready to Elevate Your Entertainment Experience
Your Ticket to Memorable Moments: Where Every Ticket Unlocks Adventure, Laughter, and Memories!
Featured Shows
All Shook Up
5/5 (24)
The Ultimate Tribute to the King of Rock 'n' Roll, Elvis Presley!
From$50.95
Together We'll Be Okay - The Musical
0/5 (0)
A mini broadway style father and daughter fun family musical
From$30.95

A-Stars Comedy Show
0/5 (0)
The Best of TV Comedians, Magic and Variety Acts
From$27.95

Aussie Heat
0/5 (0)
The Most "Hand-On" Male Revue in Las Vegas
From$57.95

Cash After Dark
0/5 (0)
The Johnny Cash Tribute Show in Las Vegas
From$37.95

All Motown
4.9/5 (43)
The Best Motown Revue in Las Vegas!
From$44.95

Frankly Frank
5/5 (34)
Frankly Frank is an intimate tribute to Frank Sinatra both the man and his music.
From$37.95
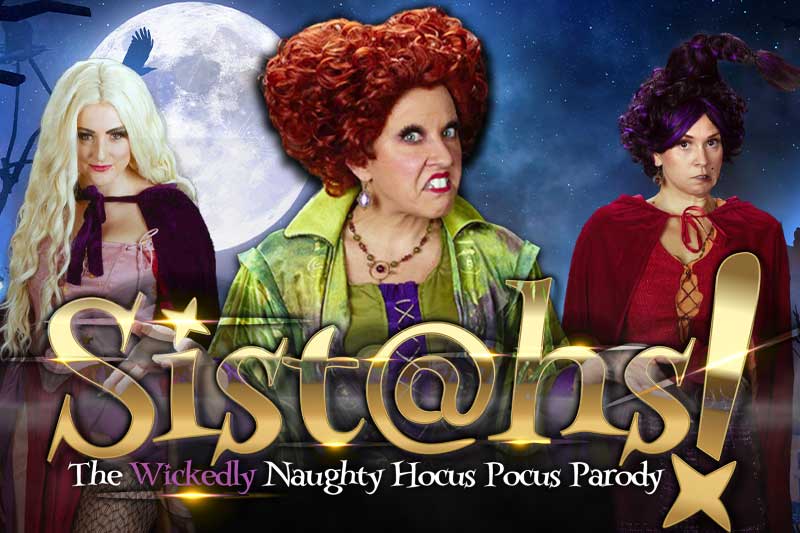
Sistahs! Hocus Pocus Parody
0/5 (0)
Returning October 2024! The Sanderson Sisters are Back in Las Vegas!
From$42.95

King of Diamonds The Neil Diamond Tribute
5/5 (7)
The Ultimate Neil Diamond Tribute show in Las Vegas
From$37.95

Flashback: Tina Turner & Friends
0/5 (0)
The Ultimate Tribute to Tina Turner and her Iconic Musical Friends
From$34.95

2024 Elvis Fest
0/5 (0)
The Officially Licensed by Elvis Presley Enterprises and Graceland - 2024 Las Vegas Elvis Fest
From$72.95